How to detect abnormal login and operation behaviors
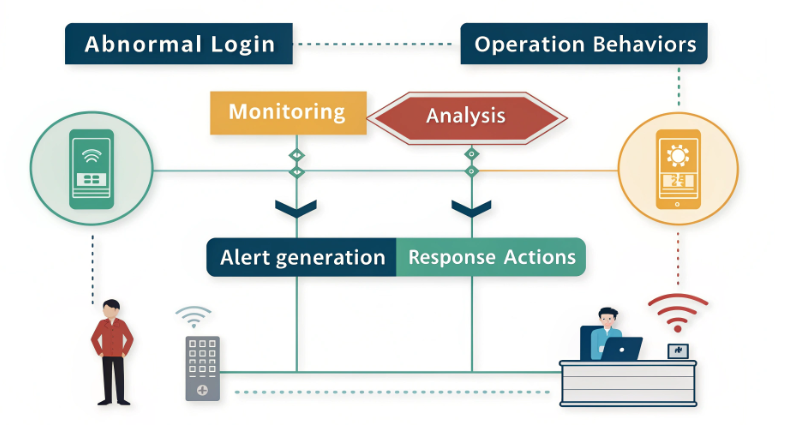
You can detect abnormal login and operation behaviors in a few ways. First, you set a baseline. Then, you watch what users do. You use anomaly detection to identify unusual activities. You also set up real-time alerts. In enterprise environments, logon events are the majority of the abnormal behaviors. Logon events account for more than 80% of all abnormal behaviors.
You need to keep security strong while also protecting privacy. Try to lower false positives. Here are common methods for detecting abnormal login activities and their advantages:
Method Type | Advantages |
|---|---|
Rule-based | Easy to use, but not good with new threats |
Statistical | Sets a baseline and finds changes |
Machine Learning | Can adapt and find hard-to-see anomalies |
Understanding User Login Behavior
Defining Normal and Abnormal Patterns
You must know what normal login looks like. Most people log in from the same places. They use the same devices. They follow a usual schedule. If you see a sudden change, pay attention. Logins from new countries or at strange times are signs of trouble. These changes can mean someone is trying to get in without permission.
Anomaly detection helps find these risks. It looks for patterns that are not normal. Older security only finds known threats. Behavioral analytics can spot new dangers. This method checks for things that are different. It helps you catch problems early. For example, logging in from two far places in minutes is a warning. Someone else may have the user’s credentials.
Behavioral analytics lets you track login behavior over time. Watching for sudden changes helps you act fast. You can keep your systems safe.
Why Monitoring Matters
You need to watch login behavior to protect your group. Sometimes, people inside can cause problems. They may not mean to, but mistakes happen. By checking normal and abnormal actions, you can stop bad things before they start. You keep important data safe.
Monitoring helps in many ways:
It finds suspicious actions, like logging in from odd places or times.
It spots risky activities, even if users do not know they are making mistakes.
It flags strange device use, like getting into systems late at night.
Evidence Point | Description |
|---|---|
Threat detection and prevention | Finds suspicious activity and stops problems before they grow. |
Preventing data breach incidents | Spots unauthorized access early and helps you secure your data quickly. |
Enhancing cybersecurity measures | Shows user actions so you can fix weak spots and respond fast. |
Establishing Baselines for Detection
Collecting User Login Data
You must collect good login data first. Start by getting identity logs for 30 days. This helps you see what normal looks like. Use tools like Pandas to clean the data. Mark each login as a success or failure. This lets you focus on real risks.
You can group users by their jobs or departments. Managers may log in at different times than staff. Look at how users use their devices. Collecting endpoint activity shows all user actions.
Here is an easy process to follow:
Get identity logs from your data lake.
Clean and add details to the data.
Label each login attempt.
Check device and endpoint activity.
Use machine learning to learn user patterns.
Identifying Behavioral Patterns
After you have your data, you can find patterns. Look for common login times, places, and devices. Track how users move through your system. Watch for changes in these patterns.
You can use different ways to spot unusual behavior. The table below shows some good methods:
Technique | Description |
|---|---|
Statistical Anomaly Detection | Finds logins that do not match normal patterns. |
Clustering Algorithms | Groups similar behaviors and finds outliers. |
Time Series Analysis | Checks for changes in user behavior over time. |
Neural Networks | Learns complex links in login data. |
Ensemble Methods | Combines models for better accuracy. |
You should update your baselines as user behavior changes. Keep watching to catch new threats. Advanced tools help you spot risks faster and keep your data safe.
Detect Abnormal Login with Anomaly Detection
Monitoring Deviations from Baseline
To find abnormal login activity, you must know what normal looks like. AI-powered security tools help by learning from user activity logs and network traffic. These tools learn your group’s usual patterns. They watch how users log in, where they log in from, and which devices they use. The system keeps checking and updating user profiles as people change their habits.
You can check for changes from normal by following these steps:
Gather data from every user session.
Use pattern recognition to find normal and strange data access.
Make statistical models that show typical user behavior.
Change baselines when users act differently.
If you see odd login patterns, like someone logging in from a new country or opening important files at weird times, you should look into it. AI systems will flag these strange actions for you. They help you spot changes in user behavior and find problems before they get worse. This way, you can find abnormal user activities more easily and lower the chance of missing something suspicious.
AI and Analytics for Anomaly Detection
AI and analytics are very helpful for finding abnormal login events. Old methods use fixed rules, but AI-based detection can change as new threats appear. You can use AI to look at lots of data and notice small changes that old systems might not see.
Here are the main types of anomalies you might notice:
Point anomalies: One login from a place you do not expect.
Contextual anomalies: A user goes into financial systems at a strange time.
Collective anomalies: Many failed logins, then a successful one from a new device.
You can also see other signs, like logging in from new devices or using systems late at night. These signs can mean someone is doing something wrong or sneaky.
The table below shows how traditional and AI-based anomaly detection are different:
Feature | Traditional Methods | AI-Based Methods |
|---|---|---|
Adaptability | Needs updates often | Changes on its own |
Accuracy | Only as good as its rules | Learns from data for better results |
Handling Complex Data | Has trouble with tricky data | Works well with complex situations |
Detection of Subtle Anomalies | Misses small problems | Finds small problems with context |
Infrastructure Requirements | Needs less computer power | Needs more computer power |
AI-based systems help you find abnormal logins and bad actions faster. They look at data right away to spot threats as they happen. You can connect these systems to other security tools, like vulnerability scanners and session monitors. This setup gives you more protection and helps you act fast when someone tries to log in without permission.
Real-Time Alerts for Unauthorized Access
You need real-time monitoring to keep your systems safe from people who should not get in. Real-time alerts tell you right away if someone tries to break in or do something strange with your data. These alerts help you follow rules, like PCI-DSS, which say you must find and report unauthorized changes.
The table below explains how real-time alerts work in big companies:
Evidence Description | Details |
|---|---|
Compliance Requirement | Real-time alerts help you follow rules by warning you about changes you did not allow. |
Tool Functionality | Tools like Qualys FIM show who made changes and when, so you can act quickly. |
Alert Customization | You can set rules to group similar events and alert the right people for better control. |
AI-powered security software can spot people in restricted areas right away. You can get alerts on different devices, so your security team always knows what is happening. This helps you react fast to strange logins and odd user sessions.
You should also check how well your detection system works. Use things like precision, recall, and F1-score to see if your system finds real threats and avoids false alarms. High precision means you get fewer false alarms. High recall means you catch most bad actions.
Implementation Tips and Reducing False Positives
Recommended Tools and Platforms
There are many tools that help find threats and lower false alarms. New platforms let you watch what users do and spot problems fast. Here are some easy tips:
Set thresholds with care. This stops too many alerts and makes finding threats better.
Change or turn off alerts for harmless actions. This helps your team focus on real dangers.
Handle exceptions well. Write down actions that seem risky but are normal for your group.
Automate responses. For example, ask users to prove who they are if they log in from a new place.
Train your team. Make sure everyone knows how to use the tools and deal with alerts.
Use cloud-native systems. These tools help you check user behavior and find threats quickly.
Keep your data up to date. Update your info often so you catch new threats.
Tailoring Detection to Your Environment
Each group needs different ways to find threats. You should change your system to fit your users and risks. Watch what users do closely. Set rules for your work hours, places, and devices. Check your alerts often. Change your settings if you get too many false alarms or miss real threats. Use detection-as-code to make changes fast.
You can group users by job or department. This helps you see normal actions and spot strange ones. Update your baselines as your group grows or changes.
Privacy and Compliance Strategies
You must keep privacy safe while making security better. Good threat detection also helps you follow rules. The table below shows some important steps:
Compliance Measure | Description |
|---|---|
Unique User Identification | Make sure you know who is doing what in your system. |
Automatic Logoff | Log users out after they stop working to stop unwanted access. |
Audit Controls | Track who gets or changes important data. |
Tools for Authentication and Monitoring | Use tools to check user identity and watch what users do. |
Regular Review of Information System Activity | Use automatic checks to look at user actions often. |
Risk Analysis and Management | Use threat detection to find weak spots and make your defenses stronger. |
Best Practices and Ongoing Improvement
Addressing Evolving Threats
New threats appear every day. Attackers change how they try to get in. They look for new ways to break into your systems. You need strong strategies to spot these changes fast.
Use advanced monitoring tools. These tools watch network traffic and user actions all the time. They help you find strange patterns before they cause trouble.
Try machine learning and AI. These tools learn what normal behavior looks like. If something odd happens, they mark it as a possible threat.
Connect your detection tools with SIEM systems. This helps you find and respond to threats faster.
Use behavioral analytics. This method tracks odd file access or strange login attempts. You can stop threats right away.
Attackers use tricks like phishing emails to steal your login details. For example, someone might send a fake email asking you to change your password. If your system uses UEBA, it can spot this unusual activity and alert you quickly.
You may face other challenges too. Attackers invent new tactics. Business rules change. Data quality problems can happen. These issues make it harder to find threats. You need to stay alert and update your systems often.
Continuous Review and Model Updates
You must check your detection models often. Threats change, so your systems need to keep up. Regular updates help you catch new risks and avoid missing alerts.
Experts in other fields update their evidence maps and safety summaries every few months. They add new information as soon as it comes up. You should do the same with your security models. This keeps your detection accurate and current.
If you see too many false alarms or miss threats, check your data for mistakes or missing parts. Fixing these problems helps your system work better. By reviewing and updating your models, you keep your security strong and ready for anything.
You can find abnormal login and operation behaviors by taking simple steps. First, make a baseline for how users log in. Then, use behavioral authentication to notice changes. Watch authentication events all the time. Look at authentication data to find threats. Use behavioral authentication to catch threats early. Set up real-time alerts for authentication. Update your authentication models often. Connect behavioral authentication with other security tools. Change authentication settings to fit your group. Use behavioral authentication to check when and how users log in. Update your system often to keep it strong. Watching closely helps you spot threats quickly. Behavioral authentication makes threat detection better. Always pay attention and keep making your authentication system stronger.

