Objective
SSH keys give added security to SSH in the sense that a password need not be used when making use of SSH keys. SSH key pair comprises both a public key and a private key, both of which are a long string of characters. The public key is saved in the server to which SSH connection is to be done and the private key is stored on the system from which SSH connection is requested.
The below steps can be followed to set up SSH Key-based authentication for all Linux OS.
1. Create SSH Key pair
On the server from which SSH connection is requested, make use of the below command to generate a key pair.
# ssh-keygen -t rsaA sample output of this command will be as below:
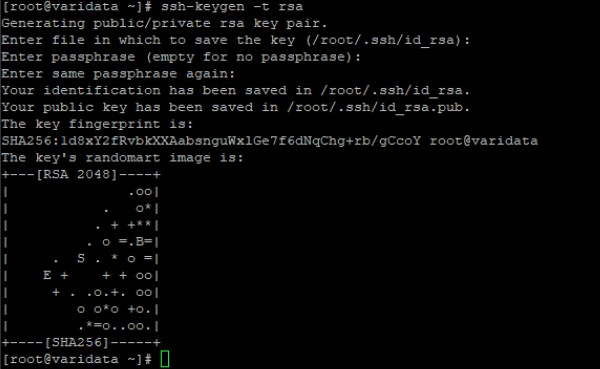
You may give a passphrase (password) at the time of key pair generation when prompted to. The passphrase adds extra security for the SSH key pair.
Once the command has been executed, the public key will be stored accordingly as id_rsa.pub and the private key as id_rsa in the path that has been specified at the time of key pair generation.
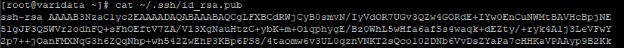
The generated public key can be viewed by using the below command:
# cat ~/.ssh/id_rsa.pubThe public key would be in the general format as below:
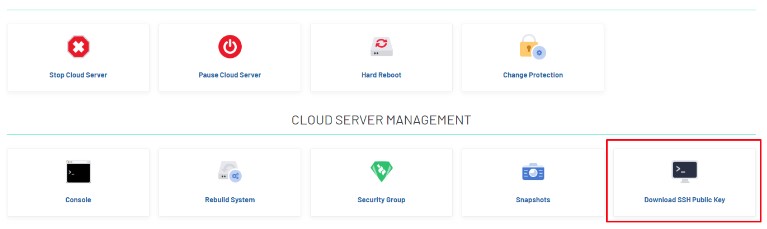
2. Download SSH Public Key of server
Or, in the Panel, there is an option to download the SSH-public-key that has been generated directly at the time of server deployment.
3. Copy the public key to the remote server
The public id_rsa.pub key needs to be copied to the server to which the SSH connection is to be made.
For this, there are two available options.
Use the ssh-copy-id command as below, where user is the username with which you are connecting to the server with IP address 123.123.123.123.
# ssh-copy-id user@123.123.123.123Note :The ssh-copy-id utility will connect to the account on the server 123.123.123.123 and then will copy the contents of the ~/.ssh/id_rsa.pub key into a file in the remote account’s home ~/.ssh directory called authorized_keys.
Copy the public key to the authorized_keys file located inside the .ssh folder in your server 123.123.123.123.
# cat ~/.ssh/id_rsa.pub | ssh user@123.123.123.123 "mkdir -p ~/.ssh && cat >> ~/.ssh/authorized_keys4. Test the SSH connection
Once the public key has been added to the server, you can test the SSH connection to the server from the computer which has the private key, using the below command.
# ssh user@123.123.123.123You may see a message like this:
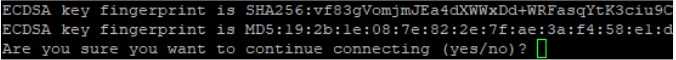
This just means that your local computer does not recognize the remote host. This will happen the first time you connect to a new host. Type yes and press ENTER to continue.
There will not be any prompt for the password. However, you may be prompted to enter the passphrase, if it had been set at the time of SSH key pair generation.
5. Disable SSH direct root login (Optional)
Once you have confirmed that the server is accessible using SSH key pair, you can proceed to disable direct root login to your server through SSH.
For this, the below steps can be followed.
Open the SSH configuration file.
# /etc/ssh/sshd_configChange the value of PermitRootLogin to no.
Restart SSH service.
# service sshd restart
